- Esxi 6.5 Patches
- Esxi 6.5 Patching Best Practices
- Esxi 6.5 Patch Download
- Esxi 6.5 Patch
- Esxi 6.5 Patch List
Name Patch Date Build; ESXi 6.5 February 2021 Patch: ESXi601: 2021-02-23: 17477841: ESXi 6.5 February 2021 Patch (Security Only) ESXi601.
- VMware vSphere 6.5 Release Notes. VMware Host Client Release Notes.
- Name Patch Date Build; ESXi 6.5 February 2021 Patch: ESXi601: 2021-02-23: 17477841: ESXi 6.5 February 2021 Patch (Security Only) ESXi601.
- To find the current version of ESXi, after I connected with PuTTY to the server, I ran this command: esxcli system version get. This shows me the current version, which in my case is ESXi 6.5.0 build 5310538. My target is to update this ESXi server to latest release which currently is ESXi 6.5.0 build 6765664, released on 4th October 2017.
Release Date: NOV 19, 2020
Build Details
| Download Filename: | ESXi650-202011002.zip |
| Build: | 17167537 |
| Download Size: | 345.2 MB |
| md5sum: | e484bb26b389d238a5dfeb88e71c4bcb |
| sha1checksum: | 4dbbee48df59dcd305735d828d5f998bfc4a32c1 |
| Host Reboot Required: | Yes |
| Virtual Machine Migration or Shutdown Required: | Yes |
Bulletins
| Bulletin ID | Category | Severity |
| ESXi650-202011301-SG | Security | Critical |
Rollup Bulletin

This rollup bulletin contains the latest VIBs with all the fixes since the initial release of ESXi 6.5.
| Bulletin ID | Category | Severity |
| ESXi650-202011002 | Security | Critical |
Esxi 6.5 Patches
Image Profiles
VMware patch and update releases contain general and critical image profiles. Application of the general release image profile applies to new bug fixes.
| Image Profile Name |
| ESXi-6.5.0-20201103001-standard |
| ESXi-6.5.0-20201103001-no-tools |
Esxi 6.5 Patching Best Practices
For more information about the individual bulletins, see the Download Patches page and the Resolved Issues section.
Patch Download and Installation
The typical way to apply patches to ESXi hosts is through the VMware vSphere Update Manager. For details, see the About Installing and Administering VMware vSphere Update Manager.
ESXi hosts can be updated by manually downloading the patch ZIP file from the VMware download page and installing the VIB by using the esxcli software vib command. Additionally, the system can be updated using the image profile and the esxcli software profile command.
For more information, see the vSphere Command-Line Interface Concepts and Examples and the vSphere Upgrade Guide.
Resolved Issues
The resolved issues are grouped as follows.
ESXi650-202011301-SG| Patch Category | Security |
| Patch Severity | Critical |
| Host Reboot Required | Yes |
| Virtual Machine Migration or Shutdown Required | Yes |
| Affected Hardware | N/A |
| Affected Software | N/A |
| VIBs Included |
|
| PRs Fixed | N/A |
| CVE numbers | CVE-2020-4004, CVE-2020-4005 |
This patch updates the esx-base, esx-tboot, vsan, and vsanhealth VIBs to resolve the following issues:
VMware ESXi contains a use-after-free vulnerability in the XHCI USB controller. A malicious actor with local administrative privileges on a virtual machine might exploit this issue to execute code as the virtual machine's VMX process running on the host. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4004 to this issue. For more information, see VMSA-2020-0026.
VMware ESXi contains a privilege-escalation vulnerability that exists in the way certain system calls are being managed. A malicious actor with privileges within the VMX process only, might escalate their privileges on the affected system. Successful exploitation of this issue is only possible when chained with another vulnerability. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4005 to this issue. For more information, see VMSA-2020-0026.
| Profile Name | ESXi-6.5.0-20201103001-standard |
| Build | For build information, see Patches Contained in this Release. |
| Vendor | VMware, Inc. |
| Release Date | November 19, 2020 |
| Acceptance Level | PartnerSupported |
| Affected Hardware | N/A |
| Affected Software | N/A |
| Affected VIBs |
|
| PRs Fixed | N/A |
| Related CVE numbers | CVE-2020-4004, CVE-2020-4005 |
This patch updates the following issues:
VMware ESXi contains a use-after-free vulnerability in the XHCI USB controller. A malicious actor with local administrative privileges on a virtual machine might exploit this issue to execute code as the virtual machine's VMX process running on the host. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4004 to this issue. For more information, see VMSA-2020-0026.
VMware ESXi contains a privilege-escalation vulnerability that exists in the way certain system calls are being managed. A malicious actor with privileges within the VMX process only, might escalate their privileges on the affected system. Successful exploitation of this issue is only possible when chained with another vulnerability. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4005 to this issue. For more information, see VMSA-2020-0026.
| Profile Name | ESXi-6.5.0-20201103001-no-tools |
| Build | For build information, see Patches Contained in this Release. |
| Vendor | VMware, Inc. |
| Release Date | November 19, 2020 |
| Acceptance Level | PartnerSupported |
| Affected Hardware | N/A |
| Affected Software | N/A |
| Affected VIBs |
|
| PRs Fixed | N/A |
| Related CVE numbers | CVE-2020-4004, CVE-2020-4005 |
This patch updates the following issues:
VMware ESXi contains a use-after-free vulnerability in the XHCI USB controller. A malicious actor with local administrative privileges on a virtual machine might exploit this issue to execute code as the virtual machine's VMX process running on the host. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4004 to this issue. For more information, see VMSA-2020-0026.
VMware ESXi contains a privilege-escalation vulnerability that exists in the way certain system calls are being managed. A malicious actor with privileges within the VMX process only, might escalate their privileges on the affected system. Successful exploitation of this issue is only possible when chained with another vulnerability. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-4005 to this issue. For more information, see VMSA-2020-0026.
Release Date: MAY 28, 2020
Build Details
| Download Filename: | ESXi650-202005001.zip |
| Build: | 16207673 |
| Download Size: | 343.3 MB |
| md5sum: | 273fbaf2d20172ad0b6f61f11933d38b |
| sha1checksum: | 08cc768779b7f6a0805cbae5953d034f380ab626 |
| Host Reboot Required: | Yes |
| Virtual Machine Migration or Shutdown Required: | Yes |
Bulletins

| Bulletin ID | Category | Severity |
| ESXi650-202005401-SG | Security | Important |
Rollup Bulletin
This rollup bulletin contains the latest VIBs with all the fixes since the initial release of ESXi 6.5.
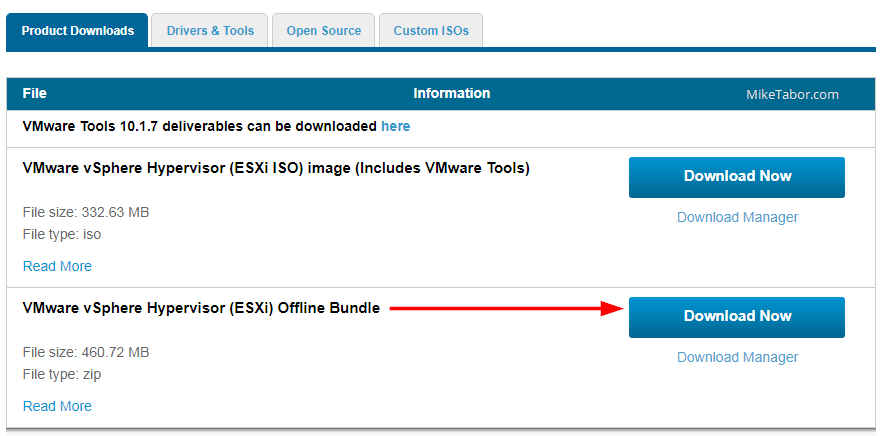
Esxi 6.5 Patch Download
| Bulletin ID | Category | Severity |
| ESXi650-202005001 | Security | Important |
Image Profiles
VMware patch and update releases contain general and critical image profiles. Application of the general release image profile applies to new bug fixes.
| Image Profile Name |
| ESXi-6.5.0-20200504001-standard |
| ESXi-6.5.0-20200504001-no-tools |
For more information about the individual bulletins, see the Download Patches page and the Resolved Issues section.
Patch Download and Installation
The typical way to apply patches to ESXi hosts is through the VMware vSphere Update Manager. For details, see the About Installing and Administering VMware vSphere Update Manager.
ESXi hosts can be updated by manually downloading the patch ZIP file from the VMware download page and installing the VIB by using the esxcli software vib command. Additionally, the system can be updated using the image profile and the esxcli software profile command.
For more information, see the vSphere Command-Line Interface Concepts and Examples and the vSphere Upgrade Guide.
Resolved Issues
The resolved issues are grouped as follows.
ESXi650-202005401-SG| Patch Category | Security |
| Patch Severity | Important |
| Host Reboot Required | Yes |
| Virtual Machine Migration or Shutdown Required | Yes |
| Affected Hardware | N/A |
| Affected Software | N/A |
| VIBs Included |
|
| PRs Fixed | N/A |
| Related CVE numbers | CVE-2020-3958 |
This patch updates the esx-base, vsan, esx-tboot and vsanhealth VIBs to update the following issue:
ESXi has a denial-of-service vulnerability in the shader functionality. Attackers with non-administrative access to a virtual machine might exploit this issue to fail the VMX process of the virtual machine, leading to a denial of service condition. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-3958 to this issue. For more information, see VMSA-2020-0011.
| Profile Name | ESXi-6.5.0-20200504001-standard |
| Build | For build information, see the top of the page. |
| Vendor | VMware, Inc. |
| Release Date | May 28, 2020 |
| Acceptance Level | PartnerSupported |
| Affected Hardware | N/A |
| Affected Software | N/A |
| Affected VIBs |
|
| PRs Fixed | N/A |
| Related CVE numbers | CVE-2020-3958 |
ESXi has a denial-of-service vulnerability in the shader functionality. Attackers with non-administrative access to a virtual machine might exploit this issue to fail the VMX process of the virtual machine, leading to a denial of service condition. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-3958 to this issue. For more information, see VMSA-2020-0011.
Esxi 6.5 Patch
| Profile Name | ESXi-6.5.0-20200504001-no-tools |
| Build | For build information, see the top of the page. |
| Vendor | VMware, Inc. |
| Release Date | May 28, 2020 |
| Acceptance Level | PartnerSupported |
| Affected Hardware | N/A |
| Affected Software | N/A |
| Affected VIBs |
|
| PRs Fixed | N/A |
| Related CVE numbers | CVE-2020-3958 |
Esxi 6.5 Patch List
ESXi has a denial-of-service vulnerability in the shader functionality. Attackers with non-administrative access to a virtual machine might exploit this issue to fail the VMX process of the virtual machine, leading to a denial of service condition. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the identifier CVE-2020-3958 to this issue. For more information, see VMSA-2020-0011.